Identify vulnerabilities. Validate security. Reduce risk.
Red Team Cockpit is an enterprise red team and penetration testing platform designed to give companies full visibility into security testing, risk exposure, and remediation progress.
Centralize assessments, track findings in real time, and transform technical results into measurable business impact - all in one structured platform.
The cybersecurity challenges companies face
Security leaders don't struggle with a lack of findings - they struggle with visibility, prioritization, and measurable progress.
These are the operational gaps that slow down most security programs:
From pentest reports to real security outcomes.

Security assessments that drive real improvement
Red Team Cockpit transforms security assessments into structured, trackable, and business-aligned security programs. More than a PDF report - gain continuous visibility, risk-based prioritization, and centralized remediation management.
Actionable Security Reporting
Executive-ready summaries for leadership. Technical detail for IT. Clear remediation guidance for operations.
Ensure every stakeholder understands what to fix and why
Risk-Based Vulnerability Prioritization
Every finding includes CVSS scoring, business impact context, and effort estimates - so you focus resources where they reduce risk most.
Align remediation efforts with real business risk
Real-Time Assessment Visibility
Track penetration testing progress as it happens. Monitor findings, status updates, and remediation tracking in a centralized dashboard.
Eliminate blind spots between kickoff and final report
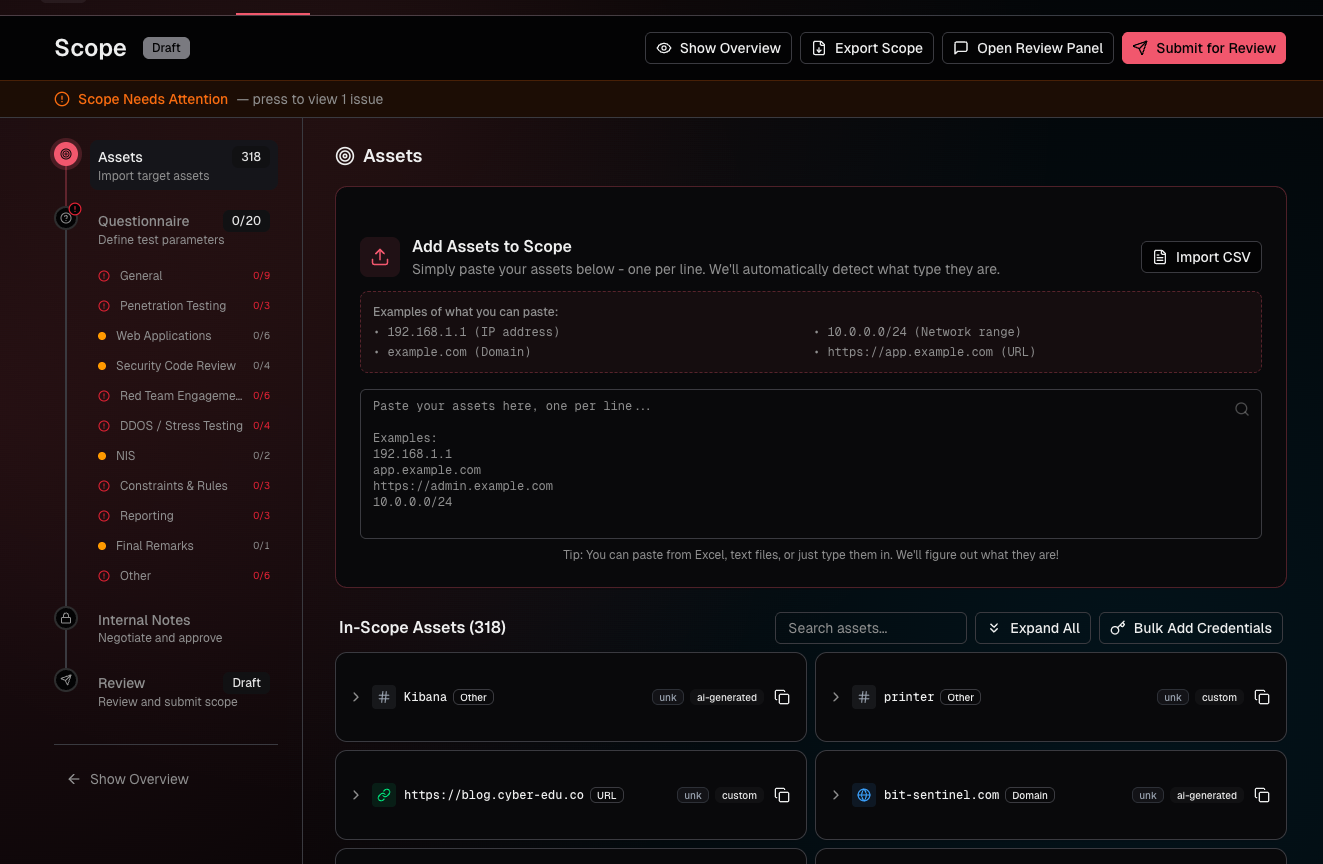
Structured Scope & Governance Control
Define and approve testing scope collaboratively. Maintain a documented audit trail for compliance and governance requirements.
Reduce scope creep and compliance risk
Continuous Remediation Tracking
Security doesn't stop at the report. Track vulnerability remediation progress and validate improvements over time.
Demonstrate measurable security improvement
Enterprise-Grade Security & Compliance
Your vulnerability data is sensitive. We protect it with enterprise-grade encryption, API security controls, and detailed audit logging.
Maintain security, integrity, and regulatory readiness
Comprehensive penetration testing & red team services
From web applications and APIs to cloud infrastructure and internal networks, we deliver enterprise-grade security testing aligned to your business risk, compliance requirements, and threat landscape.
Choose the right penetration testing methodology based on your objectives, exposure, and security maturity.
Security Testing Approaches
We tailor each engagement to your threat model, risk appetite, and security maturity.
Black Box
No prior knowledge - simulates a real external attacker
Best for: External threat simulation
Grey Box
Partial information like user accounts or network diagrams
Best for: Balanced depth & realism
White Box
Full access to code, architecture, and credentials
Best for: Maximum vulnerability discovery
Red Team
Full-scope adversary simulation including social engineering
Best for: Testing your entire security program
Specialized Penetration Testing Services
Web Application Penetration Testing
Comprehensive testing aligned with OWASP Top 10 and modern application security risks.
- Authentication & session management
- Injection vulnerabilities (SQL, XSS, etc.)
- Business logic flaws
- API security validation
Network & Infrastructure Penetration Testing
Security assessment of internal and external infrastructure environments.
- Network vulnerability analysis
- Configuration review
- Active Directory testing
- Firewall and segmentation validation
Cloud Security Penetration Testing
AWS, Azure, and GCP security testing focused on misconfigurations, identity risks, and compliance gaps.
- IAM policy review
- Storage security (S3, Blob, etc.)
- Network segmentation
- Compliance alignment
API & Microservices Security Testing
Focused testing of REST, GraphQL, and microservices architectures.
- Authentication & authorization validation
- Rate limiting and abuse prevention
- Data exposure risks
- Business logic testing
Mobile Application Penetration Testing
Security validation of iOS and Android applications and backend services.
- Local data storage security
- Network communication analysis
- Authentication flow validation
- Platform-specific risk assessment
Social Engineering & Human Risk Testing
Evaluate the human layer of your security program through controlled simulations.
- Phishing campaigns
- Vishing (voice phishing)
- Physical access testing
- Security awareness metrics
How our penetration testing process works
A structured, enterprise-grade cybersecurity testing process designed to deliver measurable risk reduction with minimal business disruption.
Scope Together
Define what gets tested through our collaborative platform. Clear boundaries, approved upfront.
Expert Testing
Our certified testers simulate real-world attacks. Track progress in real-time.
Clear Report
Receive a comprehensive report with prioritized findings and actionable remediation.
Track & Verify
Manage remediation, request re-tests, and demonstrate improvement over time.
Your security data, protected
Your security data is mission-critical. Our cybersecurity platform is built with enterprise-grade security controls to protect sensitive vulnerability data, penetration testing findings, and compliance information - at every stage.
We apply the same rigorous standards we use to secure our own infrastructure, ensuring confidentiality, integrity, and availability for your organization.
Built for Secure Cybersecurity Operations
Enterprise-grade controls protecting your most sensitive data.
- End-to-end AES-256 encryption for data in transit and at rest
- Multi-factor authentication (MFA) enforced for all users
- IP allowlisting and network access controls
- Comprehensive audit logging and activity monitoring
- Secure credential management and vaulting
- Flexible data residency and compliance-aligned hosting options
Platform Security Controls at a Glance
Enterprise-grade encryption protecting sensitive cybersecurity data.
Continuous monitoring and security hardening to safeguard platform availability.
Complete, traceable activity logs to support governance and incident investigations.
Granular, least-privilege access management aligned with enterprise security policies.